On This Page: [hide]
Do you ever wonder how the websites you visit keep your information safe? In this digital age, understanding the protocols that protect us online is essential. This article dives into the differences between HTTP and HTTPS, shedding light on why the ‘S’ for ‘Secure’ matters more than you might think.
Whether you’re a website owner looking to migrate from HTTP to HTTPS or a user curious about the padlock icon in your browser’s address bar, you’ll find valuable insights and practical tips to navigate the secure side of the web effectively.
Understanding the Basics of HTTP and HTTPS
At its core, HTTP (Hypertext Transfer Protocol) serves as the foundation for data communication on the World Wide Web, enabling the fetching of resources, such as HTML documents. It’s like the road your data travels on when moving from one point on the internet to another.
HTTPS, or HTTP Secure, builds upon this by incorporating an additional layer of security through SSL/TLS encryption. This is akin to adding a secure tunnel around that road, where only authorized users can access the data.
When you visit a website using HTTP, the data transferred between your browser and the website is sent in plain text. This can potentially expose sensitive information to anyone who might be watching the network. HTTPS combats this risk by encrypting the data during transfer, significantly reducing the chance of interception by malicious actors. This is why websites that handle sensitive information, such as credit card details and personal information, use HTTPS to safeguard user data.
Why HTTPS Is Essential for Your Website’s Security
In today’s digital age, ensuring website security is not optional; it’s a necessity. HTTPS plays a critical role in protecting websites from attacks and safeguarding user data. The encryption provided by HTTPS protects data integrity and privacy by securing data transfer from potential interceptors. This means that any information a user submits on your site is encrypted, drastically reducing the risk of unauthorized access or theft.
Google has also recognized the importance of HTTPS, using it as a ranking signal to prioritize secure websites in search results. This shift emphasizes the importance of adopting HTTPS not only for security but also as an SEO strategy. By switching to HTTPS, website owners signal to their users and search engines that they value security, thereby earning trust and potentially improving search rankings.
Comparing HTTP and HTTPS: What’s the Difference?
The fundamental difference between HTTP and HTTPS lies in the ‘S’ in HTTPS, which stands for ‘Secure’. While HTTP data is transferred in plain text, making it easy for eavesdroppers to intercept and read the information, HTTPS encrypts the data transfer, making it unreadable to anyone except the intended recipient. This encryption process uses SSL/TLS protocols to create a secure channel over an insecure network, ensuring the safety and integrity of the transferred data.
Another key difference is how browsers handle these protocols. Browsers indicate an HTTPS connection with a padlock icon in the address bar, reassuring users that their connection is secure. On the other hand, connections via HTTP lack this symbol, and modern browsers may even mark these sites as “Not Secure,” alerting users to the potential risk of sharing personal information.
Performance wise, older concerns about HTTPS causing slower site speeds have been mitigated with technological advances such as SPDY and HTTP/2, which optimize the performance of encrypted connections. So, the trade-off between security and speed has become negligible, making HTTPS a viable and recommended option for all websites.
In summary, the choice between HTTP and HTTPS affects a website’s security, user trust, and search engine ranking. With the increased focus on digital security and privacy, transitioning to HTTPS is more than an upgrade; it’s a critical step towards establishing a safer and more secure internet for all users.
Why Migrate from HTTP to HTTPS?
Migrating from HTTP to HTTPS is more than just a technical upgrade – it’s a commitment to user security and trust. In the early days of the internet, HTTP (Hypertext Transfer Protocol) was sufficient for the basic browsing needs.
However, with the internet’s growth into every aspect of our lives, the need for secure data transmission has never been more critical. HTTPS (HTTP Secure) adds a layer of encryption between a user’s browser and the server, making data less accessible to hackers.
Google has highlighted the importance of HTTPS for website owners by making it a ranking signal. This means that websites using HTTPS are favored in search engine results, encouraging more traffic. More traffic can translate into higher engagement, increased conversions, and, ultimately, better returns on your investment in your site.
Migrating to HTTPS also shows your commitment to safeguarding user information, which can help you stand out in an increasingly competitive digital space. It\s like putting a padlock on your users’ data, conveying a strong message of reliability and security.
The SEO Benefits of HTTPS: More Than Just Encryption
At its core, HTTPS provides encryption, which protects the data transferred between a user and the website. But its benefits extend well into the realm of Search Engine Optimization (SEO). HTTPS sites are seen as more trustworthy by search engines, which can lead to improved search rankings.
Besides the direct SEO boost, HTTPS enhances site security and user experience, leading to longer visits and lower bounce rates indirect SEO advantages. Websites that load over HTTPS can also utilize HTTP/2, a newer, faster version of the internet protocol that allows for quicker page loads, further improving the user experience and SEO.
For website owners seeking to optimize their online presence, adopting HTTPS is not just about encryption; it signifies reliability, which in turn can improve visitor satisfaction and engagement, driving up the site’s visibility and effectiveness.
How HTTPS Enhances User Trust and Data Integrity
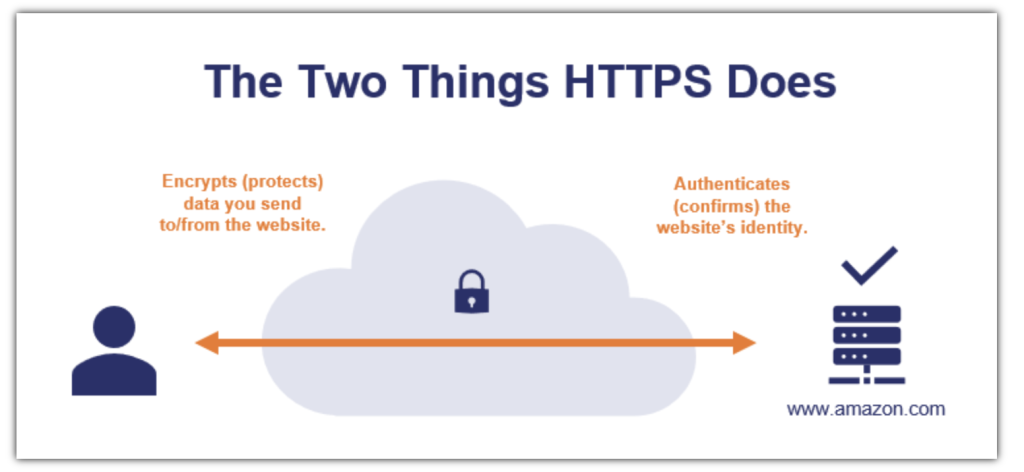
In an online environment where data breaches are not uncommon, user trust is paramount. Websites that transition from HTTP to HTTPS take an essential step in building this trust. The most visible indicator of HTTPS is the padlock icon in the browser address bar, signaling to visitors that their connection to the website is secure. This visual cue can greatly affect a user’s decision to engage further with a site, such as making a purchase or signing up for a newsletter.
Moreover, the integrity of data – ensuring that the data remains unchanged during transfer – is crucial for sensitive transactions. HTTPS ensures that data cannot be tampered with, safeguarding both the user’s information and the site’s integrity. For sites handling sensitive customer data, such as credit card numbers or personal information, HTTPS is not optional; it’s a necessity.
Preparing for Your HTTP to HTTPS Migration
Moving your website from HTTP to HTTPS is a vital step towards securing your site and building trust with your visitors. This migration not only shields the data exchanged between your site and its users but also boosts your site’s SEO ranking. Let’s dive into the key stages involved in this transition, ensuring a smooth and secure upgrade.
Choosing the Right SSL Certificate for Your Site
An SSL (Secure Sockets Layer) certificate is the backbone of the secure internet, encrypting information sent between your website and your visitor’s web browser. Picking the right SSL certificate involves understanding the different types available and matching them with your website’s needs. Generally, SSL certificates can be categorized into three main types:
- Domain Validated (DV) Certificates: These are the most basic type of SSL certification, ideal for blogs or personal websites that do not handle sensitive user information. Verification is quick, usually requiring just a domain check.
- Organization Validated (OV) Certificates: OV certificates offer a higher level of security by requiring not only domain ownership verification but also some vetting of the organization. This is a good option for websites that handle sensitive user data.
- Extended Validation (EV) Certificates: Offering the highest level of security and trust, EV certificates require a thorough verification of the business by the CA, including the legal, physical, and operational existence of the entity. This certificate is recommended for e-commerce sites and websites that handle highly confidential information.
Choosing the right SSL certificate should be based on the level of security your website needs. Remember, a secure connection reassures your visitors, potentially increasing engagement and conversions.
Backup Your Site: A Must-Do Before Making Changes
Before embarking on the migration from HTTP to HTTPS, it’s critical to back up your website fully. This precaution ensures that, should anything go astray during the transition, you can restore your site to its previous state without losing valuable data.
Implementing a comprehensive backup strategy includes:
- Database Backup: Secure a copy of your site’s database, as it contains essential elements like your posts, comments, and user information.
- File Backup: Save a copy of all the files on your site, including themes, plugins, media files, and scripts. This ensures no customization or functionality is lost during the migration.
- Test Your Backup: Before proceeding, verify that your backup works by testing it on a local setup or a staging environment. This step confirms the reliability of your backup solution.
Securing a reliable backup minimizes risks and provides peace of mind as you upgrade your site’s security. It’s a safeguard ensuring that your website’s integrity and user experience remain intact throughout the migration process.
Step-by-Step Guide to Redirect HTTP to HTTPS in .htaccess
Accessing Your .htaccess File: A Primer
Finding and editing your .htaccess file is the first step in securing your website with HTTPS. This hidden file resides in the root directory of your website and can be accessed using two main methods: via the file manager in your hosting control panel or through an FTP client like FileZilla:

If you’re using the hosting control panel, look for the file manager and navigate to your website’s root directory. It’s here you will find the .htaccess file. For those preferring FTP, connect to your server, navigate to the root directory, and locate the .htaccess file. Remember, it might be hidden, so ensure your FTP client is set to show hidden files.
Writing the Perfect .htaccess Code for HTTPS Redirection
Redirect the Entire Site to HTTPS
Securing your entire website with HTTPS is simple with the right lines of code in your .htaccess file. By adding the following:
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule ^(.*)$ https://%{HTTP_HOST}%{REQUEST_URI} [L,R=301]
This snippet checks if HTTPS is off and then redirects users to the HTTPS version of your site. This means every page on your site will automatically secure visitors with an encrypted connection.
How to Set Up HTTPS Redirection for Specific Pages Only
If you’re looking to apply HTTPS to specific pages rather than your entire site, the approach is a bit more granular. Modify the RewriteRule to target specific pages or directories:
RewriteEngine On
RewriteCond %{HTTPS} off
RewriteRule ^page-you-want-https(.*) https://%{HTTP_HOST}/page-you-want-https$1 [L,R=301]
Replace “page-you-want-https” with the actual path of the page or directory you wish to secure. This method is great for sites where only certain areas contain sensitive information, such as a checkout page or user account area.
Avoiding Common Mistakes in .htaccess Redirection
While setting up HTTPS redirection, several common pitfalls can affect your site’s functionality or security. Here are a few tips to avoid them:
- Don’t Duplicate “RewriteEngine On”: If your .htaccess already has this line, adding it again can cause issues. Always place the RewriteCond and RewriteRule lines immediately after the existing RewriteEngine On directive.
- Use Proper Flags: The [L,R=301] flags are crucial. ‘L’ stands for ‘last’, telling Apache that this rule should be the last one considered if it matches. ‘R=301’ signals a permanent redirect, helping search engines understand the move to HTTPS.
- Check for HTTPS: The RewriteCond %{HTTPS} off condition is essential. It ensures that the rule only applies if the visitor is not already using HTTPS, preventing a loop that could make your site inaccessible.
By following these guidelines, you can ensure a smooth transition to HTTPS, boosting your site’s security and SEO potential.
Verifying Your HTTP to HTTPS Redirection
In today’s online environment, ensuring that your website’s connection is secure is more important than ever. Verifying that your HTTP to HTTPS redirection is working correctly is a crucial step in this process. This not only helps in protecting your visitors’ information but also boosts your website’s credibility and search engine ranking.
Let’s dive into how you can verify that your site’s redirection from HTTP to HTTPS is functioning as intended.
Tools to Check Your HTTPS Redirection Effectiveness
Various tools available online can assist in verifying your HTTPS redirection’s effectiveness. Utilizing a Site Audit tool such as Semrush can provide a comprehensive check for technical SEO errors, including issues related to HTTPS implementation.

By navigating to the “HTTPS” section within the tool, you can easily view your site’s overall HTTPS implementation score. Moreover, such tools often offer detailed insights into any issues detected and provide guidance on how to address them. These tools are invaluable in ensuring your redirection setup is correctly configured.
- Site Audit: A site crawling tool that helps identify and fix HTTP to HTTPS redirection issues.
- SSL Checker: Verifies the SSL certificate installation and detects any potential errors with your HTTPS setup.
- Redirection Checker: Assesses if your HTTP to HTTPS redirection is properly implemented across all pages of your website.
What to Do If Your HTTPS Redirection Isn’t Working
If you discover that your HTTPS redirection isn’t working as expected, don’t panic. There are straightforward steps you can take to resolve common issues. First, ensure that your SSL certificate is properly installed and valid. Expired or incorrectly installed certificates are a frequent source of problems. Next, review your .htaccess file or server configuration to confirm that the redirection rules are correctly set up. Here, you’re looking to make sure that all requests to your HTTP pages are being properly redirected to their HTTPS counterparts.
- Check SSL Certificate Status: Make sure your SSL certificate is active, properly installed, and not expired.
- Review .htaccess or Server Configuration: Ensure your redirection rules are accurately implemented to redirect HTTP traffic to HTTPS.
- Test Redirection Across Browsers: Sometimes, issues can be browser-specific. Test your website’s redirection in various browsers to identify any inconsistencies.
Troubleshooting Tips for .htaccess Redirection Issues
Implementing .htaccess redirection from HTTP to HTTPS can sometimes lead to unexpected issues. These problems range from redirection not working at all to encountering various errors on your website. To address these, here are some troubleshooting tips that can help you ensure smooth .htaccess redirection.
Solving the Mixed Content Warning in HTTPS Sites
If you’ve successfully redirected your site to HTTPS but are still seeing “not secure” warnings, you’re likely dealing with mixed content issues. This situation occurs when a page served over HTTPS contains resources, like images or scripts, loaded over HTTP. To solve this:
- Identify Mixed Content: Use browser developer tools to find which resources are loaded over HTTP. In Chrome, right-click on your page, select “Inspect,” and go to the “Console” tab to see mixed content warnings.
- Update Resource URLs: Change the URLs of the mixed content resources to HTTPS. If external resources are not available over HTTPS, consider hosting them yourself or finding secure alternatives.
- Use Content Security Policy: Adding a Content Security Policy (CSP) header to your site can help by blocking mixed content automatically or reporting it for easy identification and resolution.
Addressing mixed content issues not only improves your site’s security but also boosts its credibility and SEO performance.
Ensuring Compatibility Across All Browsers
While redirecting HTTP to HTTPS improves security, certain browsers, particularly older ones, might experience issues if not properly managed. Here are steps to ensure your HTTPS redirection is compatible across all browsers:
- Test Across Different Browsers: After implementing your .htaccess redirection, verify it works by testing on various browsers, including older versions of Internet Explorer, Firefox, Chrome, and Safari.
- Implement HSTS Carefully: While the HSTS header can enhance security by enforcing HTTPS, it’s important to remember that not all browsers (like older versions of Internet Explorer) support it. Consider the importance of HSTS in your context and test its impact.
- Use Universal Redirection Code: Ensure the redirect code in your .htaccess file follows best practices and is broadly compatible. The provided examples in the references are generally well-supported.
Achieving a balance between usability and security is crucial. By addressing mixed content issues and ensuring cross-browser compatibility, your site will not only be secure but also deliver a better user experience.
Optimizing Your Site Post-HTTPS Migration
Migrating your website from HTTP to HTTPS is not just a trend but a significant move towards securing user data and improving your site’s authority and trustworthiness. Once you’ve made the leap to HTTPS, optimizing your site to reflect this change is crucial for maintaining SEO rankings and ensuring a seamless user experience. Let’s dive into the key steps you need to take post-migration.
Updating Your Internal Links to HTTPS
With this transition, ensuring all your internal links point to the new secure URLs is essential. Failing to update these links can lead to broken pages, negatively impacting user experience and your site’s SEO.
Here’s how to approach this update:
- Identify Insecure Links: Use a site-crawling tool to scan your site for any internal links that still use HTTP. These tools automate the detection process, saving you from the manual effort of checking each link.
- Make the Switch: Once you have a list of HTTP links, update them to HTTPS. This step is crucial for avoiding redirect chains, which can slow down your site and diminish user experience.
- Test Your Links: After updating your links, it’s important to test them to ensure they lead to the correct HTTPS pages. Broken links can hurt your SEO efforts and lead to a frustrating experience for your visitors.
By meticulously updating your internal links, you safeguard your site against SEO and usability issues, ensuring a smooth browsing experience for your visitors.
Notifying Google About the Migration to Secure Protocols
Telling Google about your shift from HTTP to HTTPS is critical for maintaining your site’s visibility and rankings in search results. Google views HTTP and HTTPS as two distinct websites, so it’s essential to inform them about your move to ensure users are directed to the secure version of your site. Follow these steps to notify Google:
- Verify Your Site in Google Search Console: If not already done, verify the encrypted version of your site in Google Search Console. This step is crucial for tracking your site’s performance in Google’s search results.
- Update Your Site’s Property Settings: In the Search Console, ensure you update your property settings to reflect the shift to HTTPS, helping Google understand which version of your site to prioritize.
- Check Your Coverage: Utilize the coverage report in Google Search Console to ensure Google can crawl and index your HTTPS site without issues. This report also helps identify any crawl errors that need addressing.
By effectively communicating your migration to Google, you help ensure a smooth transition in search rankings and visibility, minimizing potential disruptions to your site’s traffic.
Embracing HTTPS is more than just a technical update; it’s a commitment to your users’ security and privacy. By ensuring your site’s internal links are updated and Google is informed of your migration, you’re not only optimizing your site for better performance but also reinforcing its trustworthiness and authority in the digital space.
